Sep 22, 2023
Installing the provisioning agent– Implementing and Managing Identity Synchronization with Azure AD
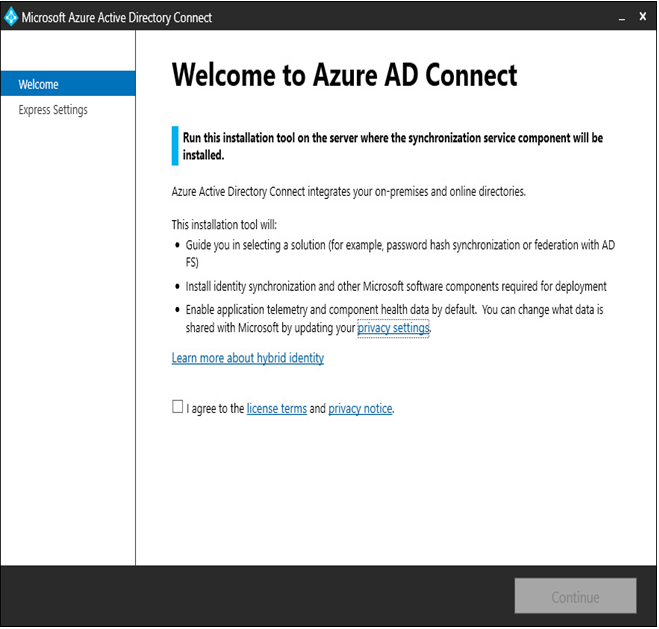
To begin installing Azure AD Connect cloud sync, follow these steps:
- Log on to a server where you wish to install the Azure AD Connect cloud sync provisioning agent.
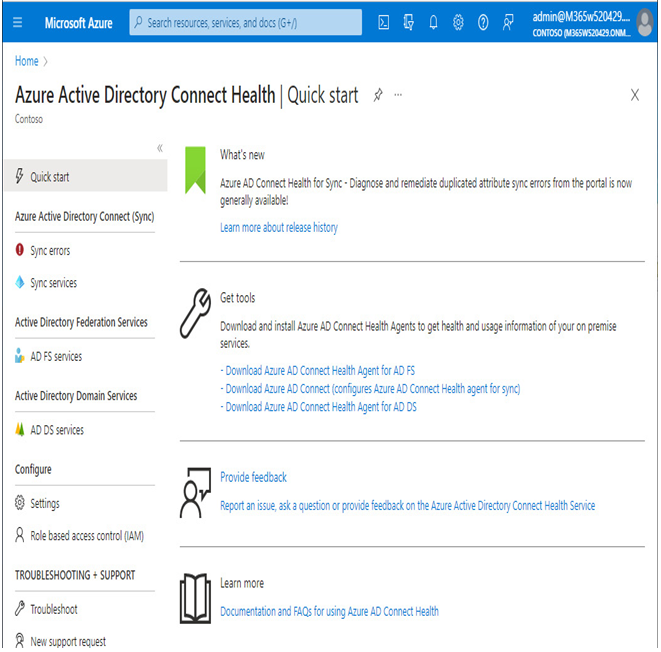
- Navigate to the Azure portal (https://portal.azure.com) and select Active Directory | Azure AD Connect.
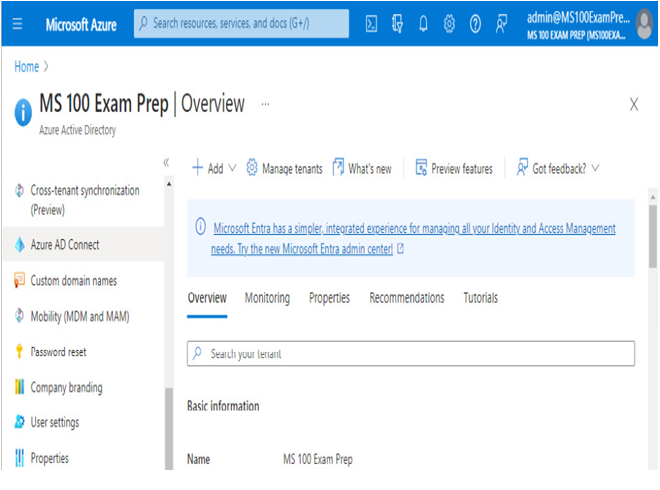
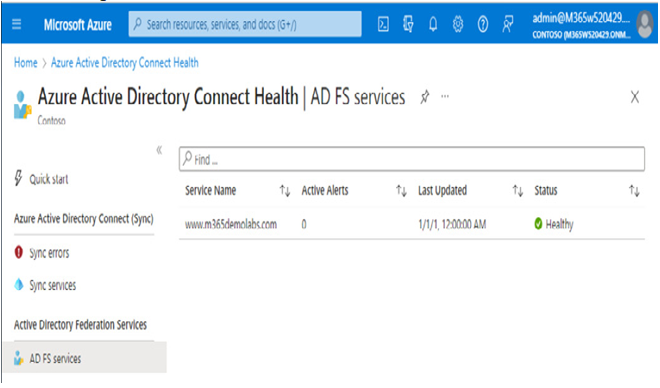
Figure 4.25 – Azure AD Connect in the Azure portal
- From the navigation menu, select Cloud sync.
- Under Monitor, select Agents.
- Select Download on-premises agent.

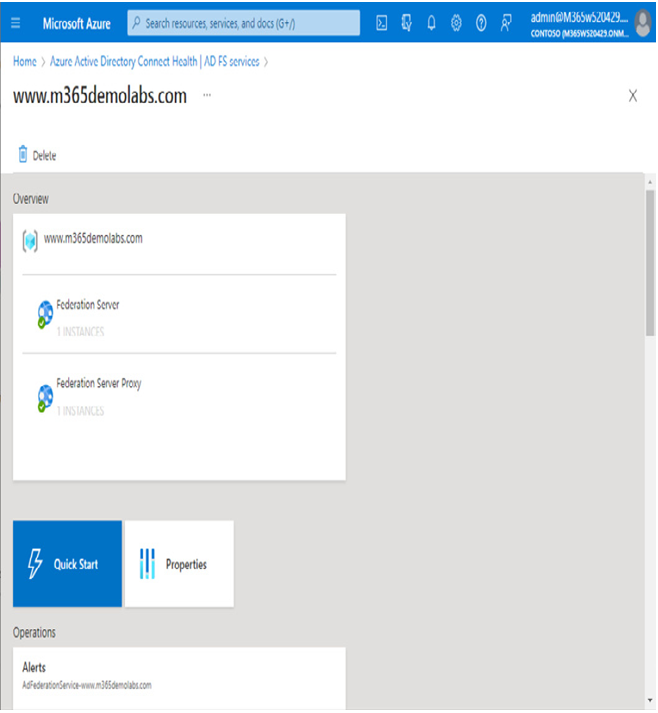
Figure 4.26 – Download on-premises agent for Azure AD Connect cloud sync
- On the Azure AD Provisioning Agent flyout, select Accept terms & download to begin the download.
- Open the AADConnectProvisioningAgentSetup.exe file to begin the installation.
- Agree to the licensing terms and click Install to deploy the Microsoft Azure AD Connect provisioning package.
- After the software installation is complete, the configuration wizard will launch. Click Next on the splash page to begin the configuration.
- On the Select Extension page, choose the HR-driven provisioning (Workday and SuccessFactors) / Azure AD Connect Cloud Sync radio button and click Next.
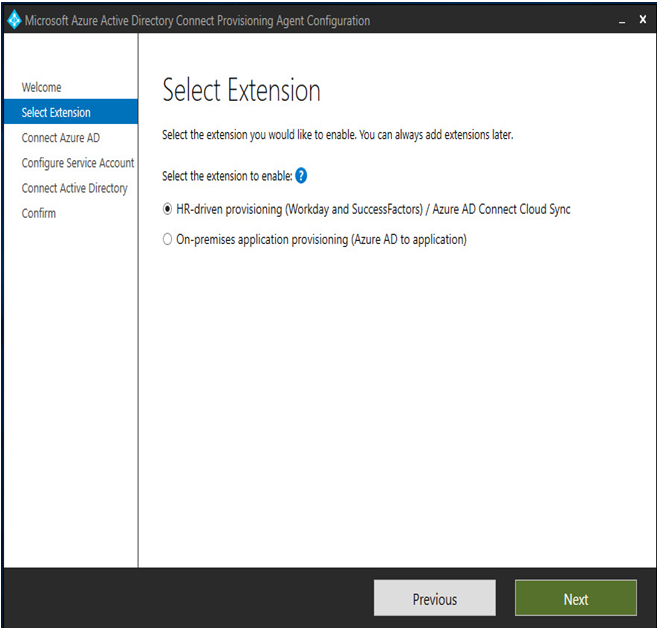
Figure 4.27 – The Azure AD Connect cloud sync Select Extension page
- On the Connect Azure AD page, click Authenticate to sign in to Azure AD.
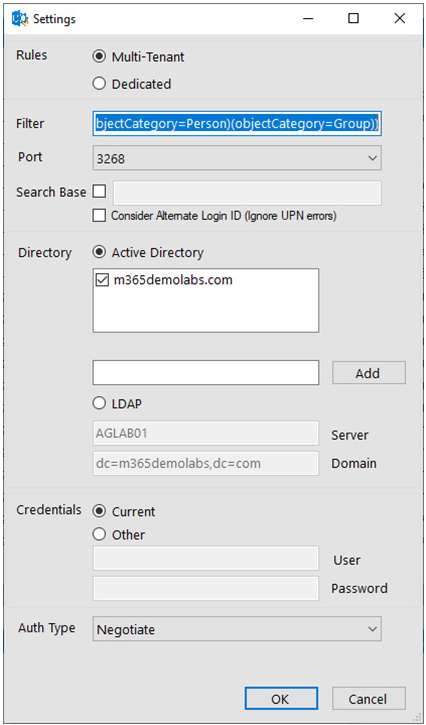
- On the Configure Service Account page, select the Create gMSA radio button to instruct the setup process to provision a new gMSA in the format of DOMAIN\provAgentgMSA. Enter either a Domain Administrator or Enterprise Administrator credential and click Next.
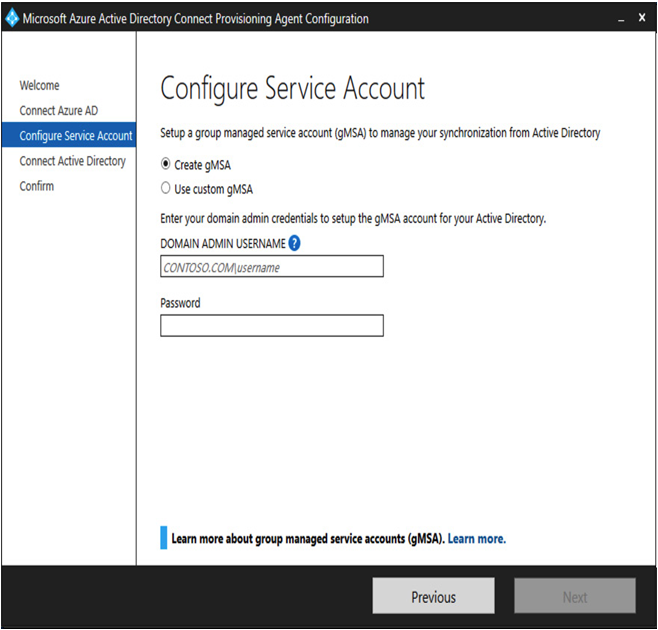
Figure 4.28 – Configuring an Azure AD Connect cloud sync service account
CREATING A CUSTOM GMSA
You can also create a gMSA if desired. The custom service account will need to be delegated permissions to read all properties on all User, inetOrgPerson, computer, device, Group, foreignSecurityPrincipal, and Contact objects, as well as being able to create and delete user objects. For more information, see https://learn.microsoft.com/en-us/azure/active-directory/cloud-sync/how-to-prerequisites?tabs=public-cloud#custom-gmsa-account.
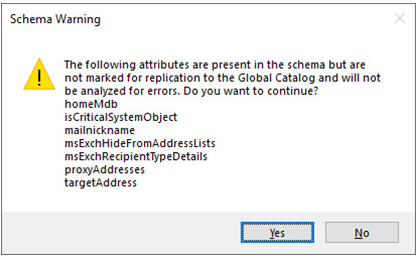
- On the Connect Active Directory page, click Add Directory and provide the domain credentials to add the directory to the configuration. When finished, click Next.
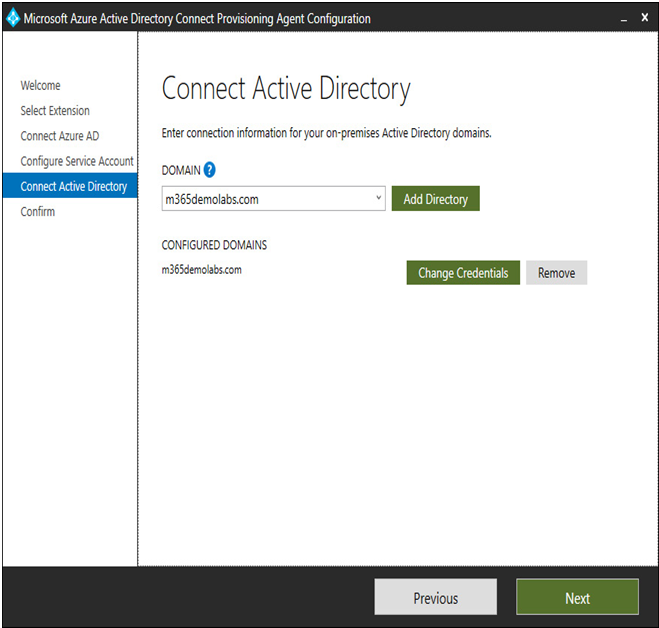
Figure 4.29 – Adding a directory to Azure AD Connect cloud sync
- Review the details on the Agent configuration page and click Confirm to deploy the provisioning agent. When finished, click Exit.
After the agent has been deployed, you will need to continue in the Azure AD portal.
More Details