Dec 7, 2023
Creating and managing users– Planning and Managing Azure AD Identities
As you’ve seen throughout this book, identity is the foundation of Azure AD. Without it, people wouldn’t be able to access services. Azure AD identity covers a broad range of objects, including cloud-only accounts, synchronized accounts, and external accounts (as well as groups, devices, and contacts).
Each of these types of objects has a purpose, and one is generally more suited to a business case than another.
In this chapter, we’re going to look at the following topics, as they relate to the MS-100 exam objectives:
- Creating and managing users
- Creating and managing guest users
- Creating and managing groups
- Managing and monitoring Microsoft 365 license allocations
- Performing bulk user management
By the end of this chapter, you should be comfortable articulating the differences between the different kinds of objects and familiar with methods for provisioning and managing them.
Let’s get started!
Creating and managing users
Creating and managing users is central to administrating an information system—whether that system is an application on a small network, an enterprise-scale directory, or a cloud service hosted by a SaaS provider. In any instance, identities are used by people, applications, and devices to authenticate and perform activities.
In the context of Azure AD, there are three core types of identity:
- Cloud-based users
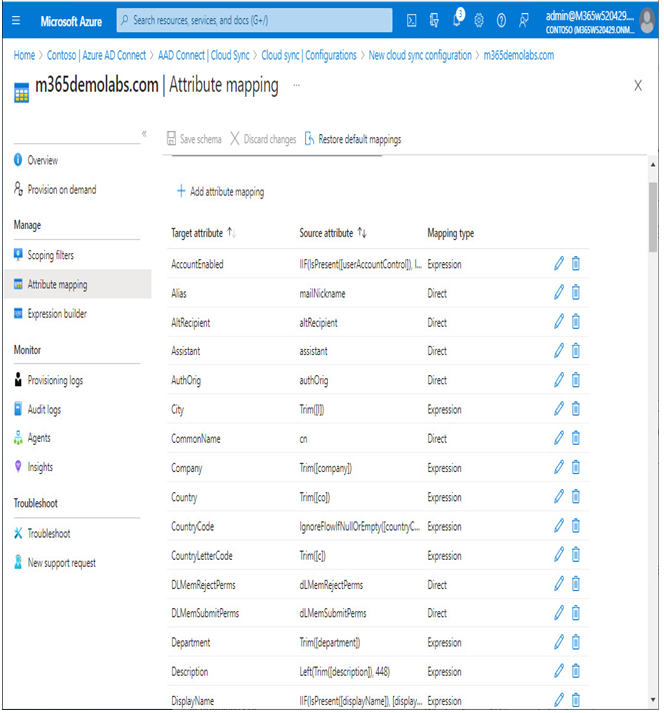
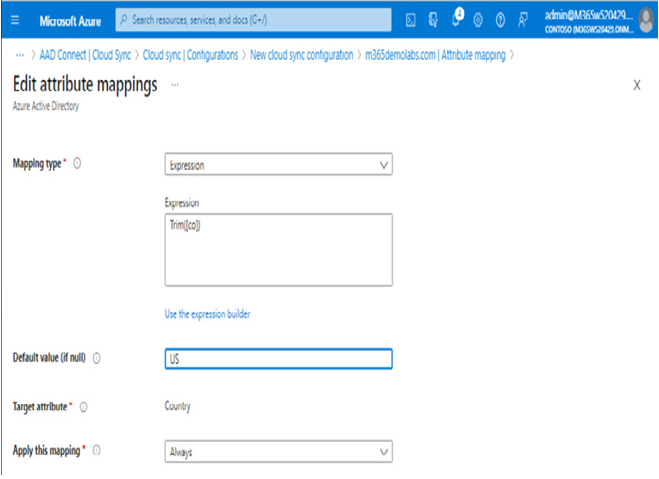
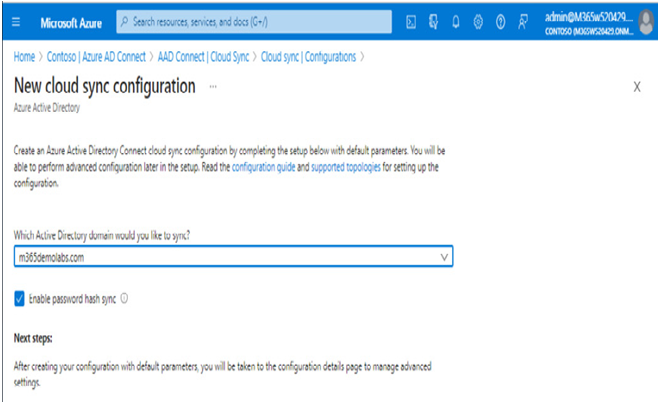
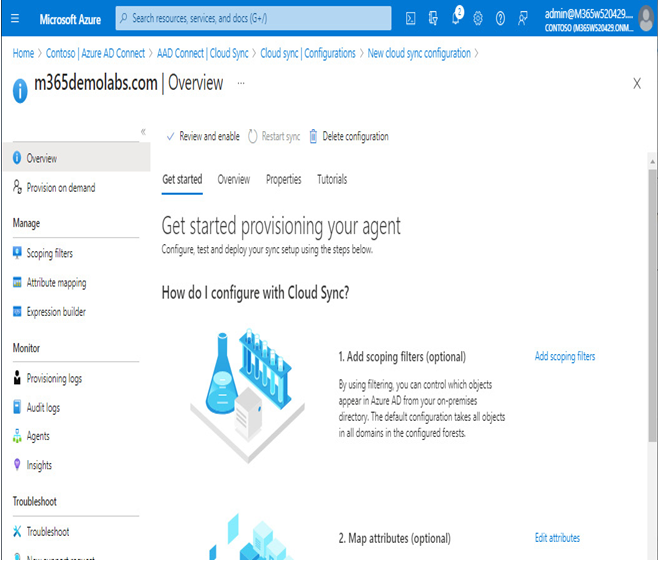
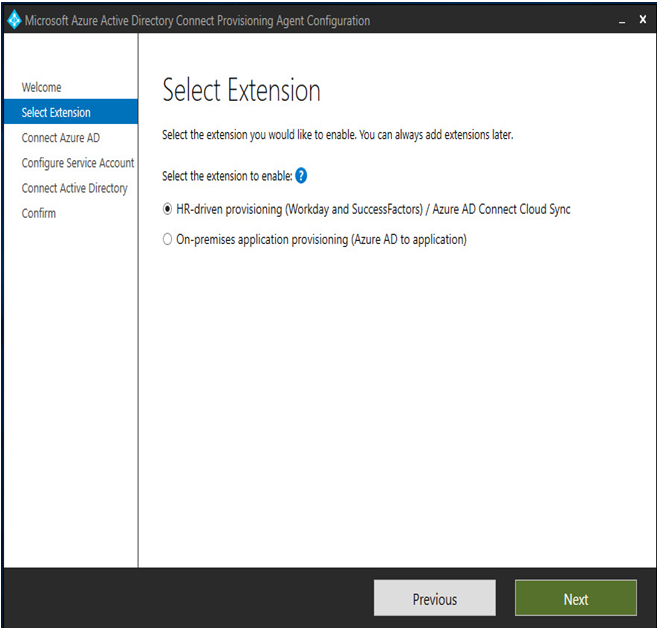
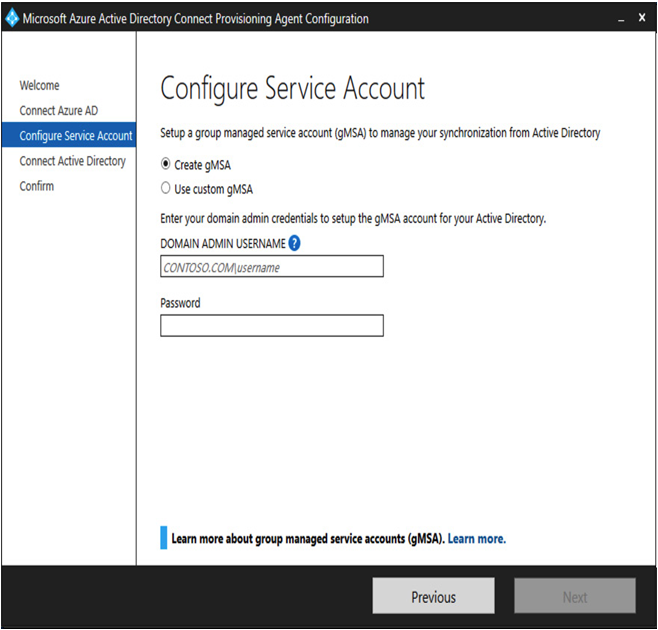
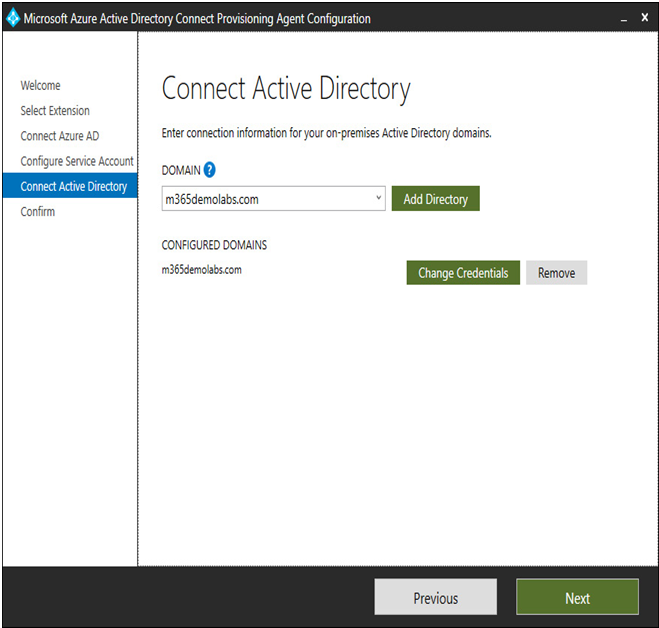
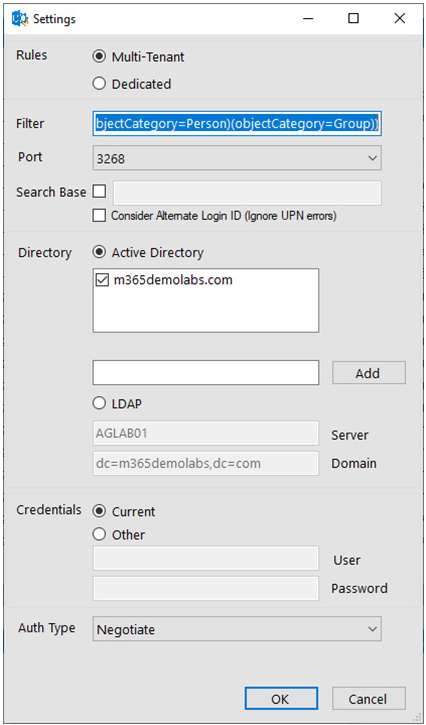
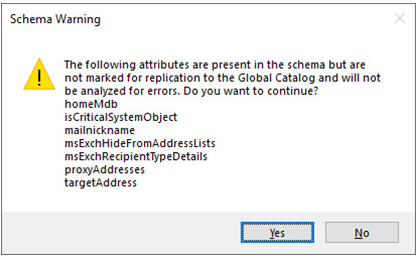
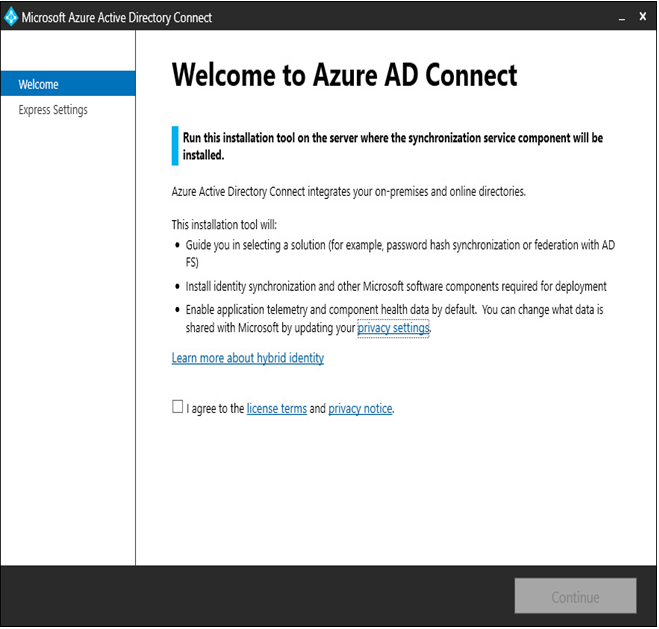
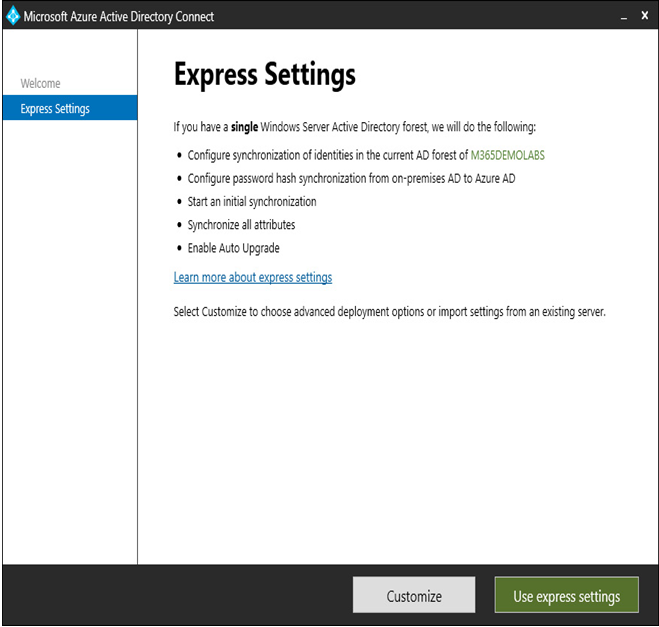
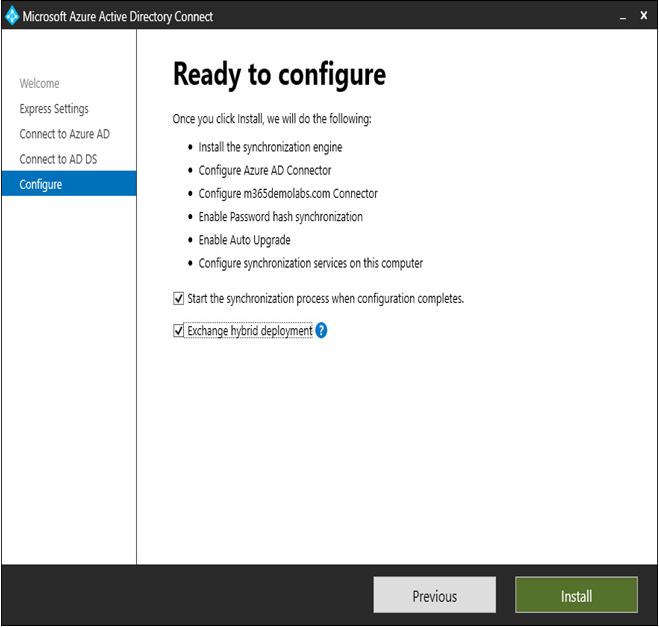
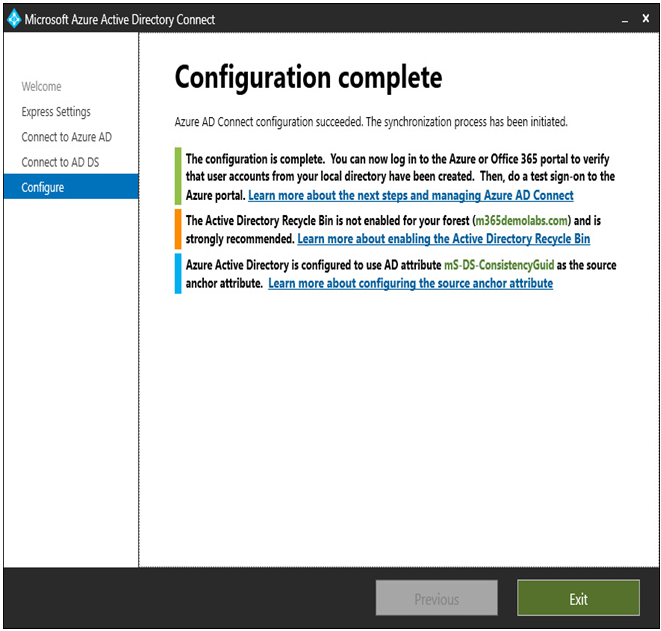
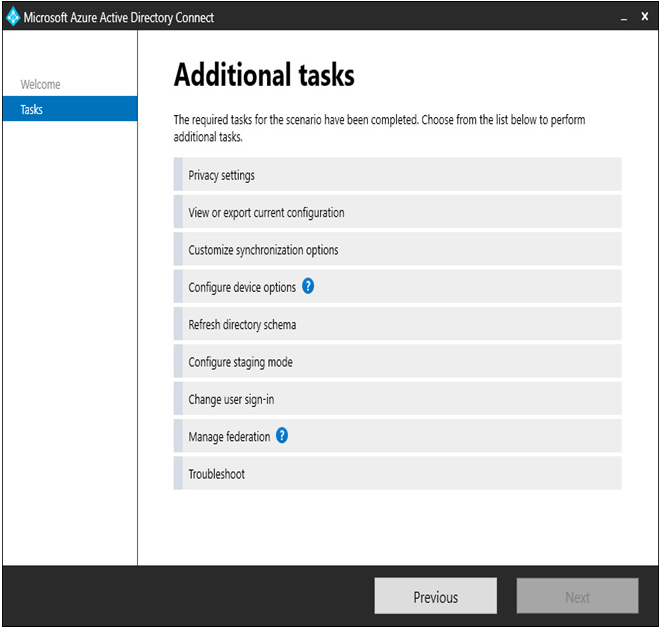
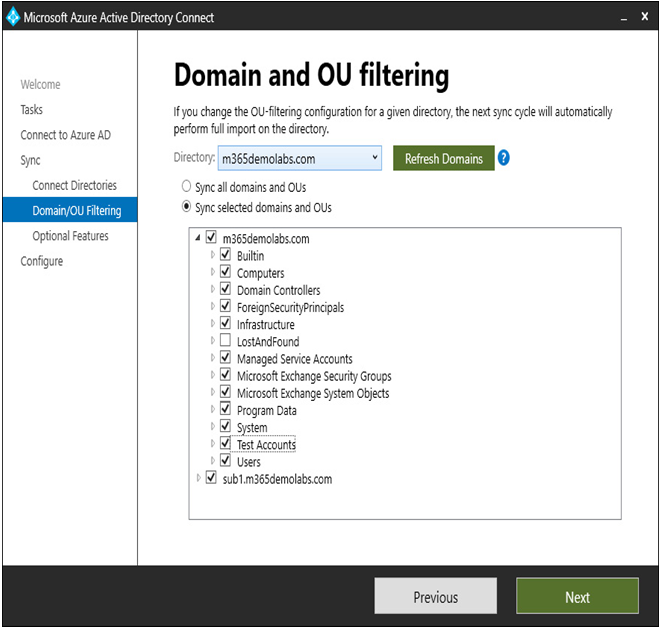
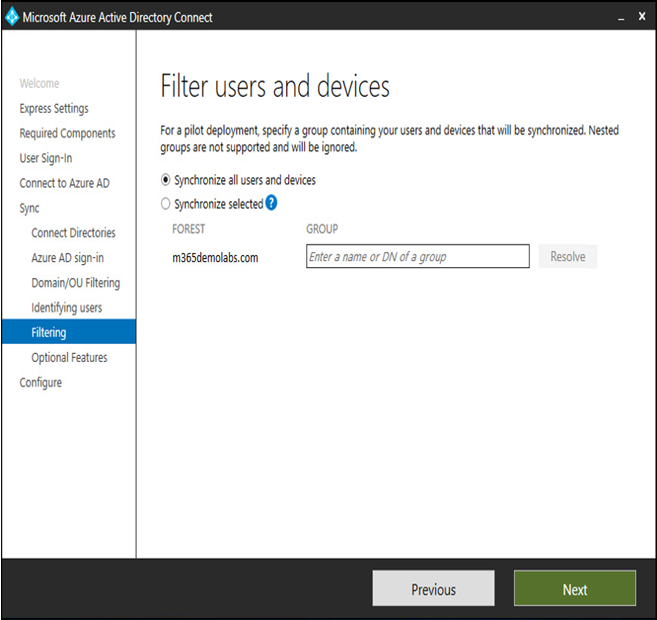
- Synchronized users
- Guest users
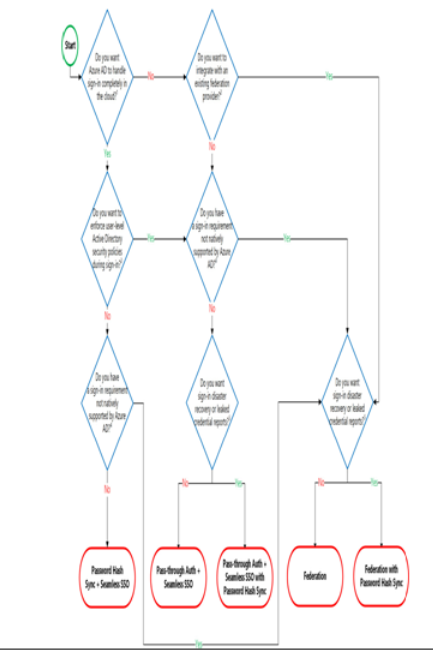
When planning out identity scenarios, it’s important to understand the benefits, features, drawbacks, or capabilities associated with each type of identity and authentication scheme—including ease of provisioning, integration with existing directory or security products, requirements for on-premises infrastructure, and network availability.
In this section, we’ll learn about managing each of these kinds of users.
More Details